The digital age started around 1980 with the Internet and the traditional industry witnessed a rapid shift to the present era which is entirely based on information technology. Slowly information started forming the foundation of every organization and businesses around the globe and it began floating freely without restriction and adequate protection, inviting several threats and encouraging hackers or people with malicious intentions to exploit it for their personal benefits.
Digital data like photos, conversations, health information, online transaction details, finances, identification number etc are the personal data or sensitive personal data that are mostly exposed to chances of being misused as these are critical information that identifies a person and reveals a lot about his privacy. And in today’s world where we like posting our lives on social media and make payments or shop on online platforms, we ourselves give away a lot of our personal data to applications or organizations.
Hence to build some kind of restrictions around this free movement of personal data and to preserve the human rights to privacy in the digital world there had been several privacy regulations or laws that were enacted and there are some which are currently getting drafted. These laws ensure robust protection to personal data through compliance with its principles.
Following is the list of some of the Privacy Regulations around the globe:

These Privacy regulations highlight certain key concepts and talk about how data could be made secured throughout its entire lifecycle.
A typical lifecycle of data or several ways of processing the data are:
1. Collection of data
2. Recording
3. Storing
4. Using
5. Analyzing
6. Disclosing
7. Transferring
8. Deleting
The diagrammatic presentation of data transfer/ movement captures the various roles who handle the data at different stages:

When the Data subject provides his personal data or sensitive information like racial origin, political views, bank account numbers, sexual orientation, to the Data Controller:
1. Data Subject’s consent is obtained for Processing his data
2. Legal obligations are fulfilled
3. Legitimate interests of the Organization and Data Subjects’ privacy rights are established
4. The Rights of Data Subject are informed like
· Right to access his own personal data
· Right to ask for deletion of data
· Right to not be subject to automated decision making
5. Data is processed in a pre-informed way and only for the required purpose
6. Data is processed ensuring all the legal obligations are met
7. Data subject is informed about the method and purpose of the processing
8. Data is made secured adequately at every stage of processing
9. Data is kept secured while transferring it to other countries for required purposes
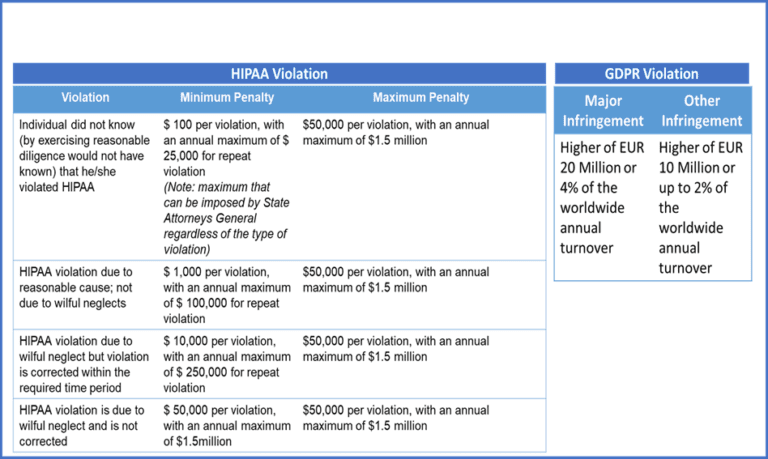
Penalties Of Violation: