Why SOC 2 Compliance is Critical for Your Organization
Most organizations are increasingly relying on cloud services to meet so many of their business needs. How an organization can know all its vendors are handling its sensitive information securely?
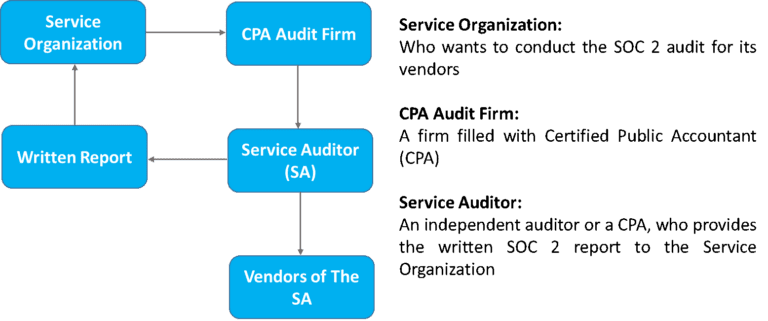
From here Service Organizational Control (SOC) 2 audit comes into the picture. SOC 2 audit provides an independent assessment of vendor controls.
What is SOC2?
SOC 2 defines the criteria for managing customer data based on the five service principles,
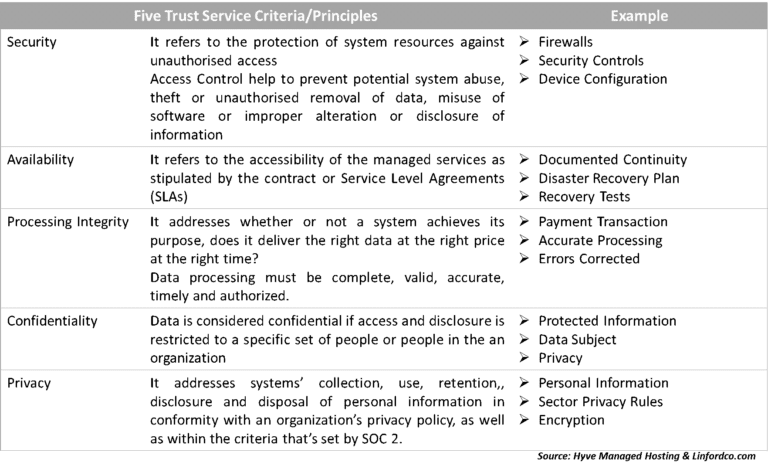
SOC2 reports are unique to each organization. These are in line with specific business practices. Each designs its own control to comply with one or more trust principles (Trust Security Criteria).
Service organizations receive SOC 2 reports to demonstrate they have certain controls in place to maintain risk less environment.
How SOC 2 Audit Works?
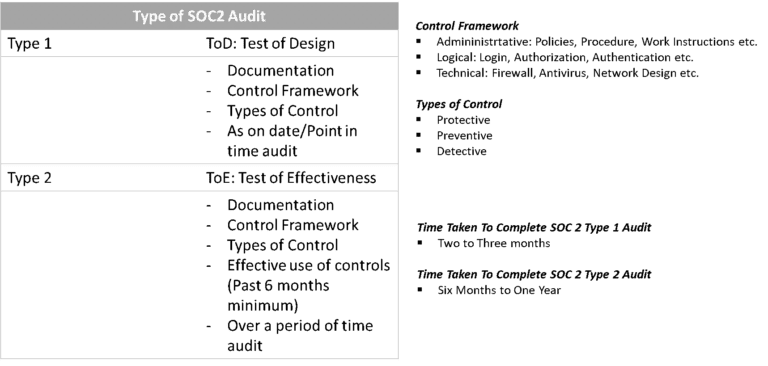
Types of SOC 2 Audit
Note
If a client has any seriousness in the work to be done, it will ask for the Type 2 audit.
Type 1 is not mandated for Type 2. Type 2 includes Type 1.
There are no guidelines have been laid out by AICPA to complete Type 1 audit before going for Type 2
Need of SOC 2 Compliant
1. Commitment to Security
SOC 2 demonstrates an organization’s strong commitment to overall IT security. The internal controls, policies, and procedures are evaluated against the industry’s best practices to ensure the protection of data.
2. Increase Authorization of Access
An organization can assure its client that the organization has met established SOC 2 criteria that ensure that the system is protected against unauthorized access (both physical and logical).
3. Efficient management of controls
Five Trust Service Criteria/Principles provide an effective baseline to evaluate the current security state of an organization. Treating one baseline set of controls allows management to be more focused and efficient in the maintenance of their control environment.
4. Secure Vendor Environment
SOC 2 provides criteria to assess vendor security. By maintaining the criteria, an organization can secure its vendor environment which, reduces the chance of security incidents from a vendor’s side.
5. Streamlined Compliance Mapping
SOC 2 provides a good number of controls for the different areas. A SOC 2 implementation helps an organization to streamlined with the following standards/frameworks,
ISO/IEC 27001:2013
ISO/IEC 27701:2019
GDPR
HIPAA
PSI DSS and many more
